I use to always recommend bitwarden to people. Now i feel like an idiot for doing so with them switching up. Ill be making the effort to move to keepassxc soon and host it myself.
They literally posted that this is a packaging bug and will be resolved.
That’s good news
Just because I didn’t see a response on this one, you might have read it already in other comments but the packaging bug is a cop out. They are still intending to migrate over to the proprietary SDK, and it will eventually become a requirement for the platform. The only difference was that at the state of the project it wasn’t supposed to be a requirement in order to compile, but they do still very intently have a restrictive license on the SDK and you aren’t allowed to use the sdk outside of the project. meaning that it has to be present for the program to work and that you’re not allowed to use it in other programs.
Why they call it a packaging bug I’m not sure because the end result is the same the package is required for the program to work and that package that is required is not GPL
That being said some other comments have gone a little bit more in detail on it and might be a little more descriptive than me
…host it?
…is there something I’ve been missing out on? Can one host a KeePass vault online? We have web apps? I only know about the Nextcloud ones. I’ve just been using syncthing and merging the conflicts when they happen.
I used to keep a copy of my kepass file in a free Dropbox account.
I mean sync it between my devices using something like sync thing
Alright does anyone have opinions on Nextcloud Passwords? There’s apps for it and it would sync to my Nextcloud.
I hate this. Bitwarden has been a good app.
It’s a packaging bug, the headline is false.
Bitwarden has been a good app.
And it still is. There’s no reason to stop using Bitwarden, and I will continue my plans to switch to Vaultwarden.
As @Krzd@lemmy.world said, it’s a packaging bug, not an actual change in license. If you read the article, it says as much in the update.
Nextcloud passwords is just a client for a KeePass vault.
I guess it’s as good or bad as that can be, but I’m sure it’s limited in functionality to KeePassxc with plugins.
Oh really? Where’s the keepass file stored? This would be very cool if so
TIL… Thanks.
EDIT: Been playing with it a bit now and if it uses keepass as the DB the advantage I see right now is that having it in Nextcloud means automatic sync, and there are several autofill and syncing apps for various OSes and password sharing and automated checks for breaches. It’s probably a better option for anyone with Nextcloud than going the Keepassxc/syncthing route.
Are you sure?
Because last time I tried that it was THE worst password manager that i ever tried in my life. I’d feel safer with the ie6 password manager
You can encrypt the entire vault and all the contents,… but imo, that should be a default setting.
Seriously, as-is, you log into Nextcloud, click on passwords and every password is literally right there. I’m sure they’re encrypted in the database but fffff.
(I tried it out on my install just now)
(I use KeePassxc mostly)
so what’s the best pw manager?
Vaultwarden is a nice self hosted bitwarden alternative
https://github.com/dani-garcia/vaultwardenSome prefer using KeepassXC and sync the database between devices
https://www.ctrl.blog/entry/keepass-vs-bitwarden-server.html+1 For KeePassXC and the KeePass ecosystem. Yes, you need to sync the database yourself, but you can use any file sharing service you like, e.g. google drive, dropbox… or selfhost something like nextcloud (like I do), which for me is actually a point in its favor.
Based on this news, I think I made the right choice back then when I decided to go with KeePass.
As someone who used to use KeePass, went to LastPass, and then Bitwarden (Vaultwarden), I finally got my non-tech literate wife to use Bitwarden. I’m concerned that KeePass might end up being more difficult if it comes down to it. I believe that KeePass had some sort of browser integration but it really has been a long time since I used it so who knows the current state. Curious how browser integration is today.
The big issue isn’t using it, it’s syncing it.
User A used KeePass to order pizza and changed the Papa John’s(heaven forbid) password while they were at it, on their desktop.
syncing: “oh! This file changed! Neat!”
User B picks up their phone and wants to order Papa John’s at work. They try, but the password isn’t right. Huh. They check KeePass. No issues. They go to change the password because they think something is wrong.
(All the while, they never thought to see if syncthing had been woken up in the background lately)
They change the password, update KeePass,
syncthing opens later, goes: "Oh, hi, User B’s phone! I have a ne- Oh! You have a new password file too!!? Small world! I’ll take both!
Now there’s two files, two users who think they both made corrections to a password, syncthing thinking nothing is wrong, and someone has to now merge the newer KeePass file over the old ones by hand and realize what happened, but the bigger problem is, no one knows anything is wrong yet and it doesn’t even take two users. This can just be you ordering on your phone after modifying on your desktop.
well, it’s just pizza.
As an example. Imagine an insurance app, or a banking app, or the DMV… And you won’t know for months down the line. It gets old.
Ah yeah, the fun of how that works. I recall that I had previously set up WebDAV to try to simplify my source of truth but I think that was just with the original KeePass app, not KeePassXC. I also wasn’t trying to share passwords among multiple people but I do recall having issues when I was using Dropbox to sync to my phone since I would have to actually make sure Dropbox had updated the copy of the file which required me opening the app at the time.
I use KeePassXC on desktop and Keepass2Android on, well, android, and sync via nextcloud. They all seem to handle syncing correctly, merging changes made on one side, or showing a notification about a conflict, and KeePassXC can definitely merge the two “conflicted copies” together reliably with a couple of clicks (yes, a no-click solution would be better, I know, but it’s not “manual”). Keepass2Android integrates directly with nextcloud and seems to handle it fine.
The situation can definitely be improved but it’s not so bad for me. Also, two different people should probably use two different database files and not share passwords ;)
Not sure how syncthing handles conflicts, it’s been many years since I tried it.
I use KeePassXC’s browser integration daily and it works pretty well with Firefox (linux), well enough that I’m not complaining, but I cannot compare it with Bitwarden cause I never used it. On Android I use Keepass2Android and works well with autofill, but again, I can’t really compare it.
Something tells me Bitwarden works better, just by virtue of being a commercially supported product, but I have no complaints with KeePassXC & Keepass2Android (KeePassDX works well on android too). Original KeePass desktop client was never great though.
Vaultwarden is Bitwarden–at least for now, this change may push them apart.
Keepass? No cross device support, you need to manage that yourself through something like Google Drive…
What do you mean “no cross device support”? KeePassXC supports Win, Mac, Linux and there are iOS and Android apps available…
As for the lack of cloud and requirement to provide your own synchronization, for some (like me) that’s a feature, not a limitation :)
Do any of the iOS or Android apps support passkeys? I looked into this a couple days ago and didn’t find any that did. (KeePassXC does.)
Keepass2Android doesn’t have it yet, but seems to be working on it
https://github.com/PhilippC/keepass2android/issues/2099Strongbox seem to have their implementation done for iPhone
https://strongboxsafe.com/updates/passkeys/From a quick search, Keepass2Android doesn’t have it, not clear if they’re working on it: https://github.com/PhilippC/keepass2android/issues/2099
KeePassDX similarly has an open issue, not clear when/if it will be implemented: https://github.com/Kunzisoft/KeePassDX/issues/1421
Good to know about Strongbox on iOS, though I’m on android so no bueno for me.
I don’t use passkeys so I don’t know. Maybe I should research into passkeys, what’s the benefit over plain old (long, randomly generated) passwords?
Ok, from a quick search, it seems passkeys rely on some trusted entity (your browser, OS, …) to authenticate you, so, yeah, I’m not sure if I like that. The FIDO alliance website is all about how easy, convenient and secure passkeys are, and nothing about how they actually work under the hood, which is another red flag for me.
I’ll stick to old-fashioned, long, secure, randomly generated passwords, thanks.
I was finally able to find some technical detail on passkeys on FIDO website, and yeah, it actually looks like it’s a real improvement over passwords: it’s simple, uses proven technology (public/private keys), and should be much more secure than passwords.
Also, nothing in the “specs” says I need to entrust my private key with the OS or a third party, which is good.
That said, it seems some OS support is required nonetheless, to show the pin / biometrics prompt (or is it?), and on android at least, I’d need to buy a new device with Android 14 to use a non-Google passkey provider…
Passkeys rely on you holding a private key. The initial design was that a device (like a browser or computer/phone) stored the private key in a TPM-protected manner, but you can also store it in a password manager.
This is more secure than a password because of the way private/public key encryption works. Your device receives a challenge encrypted with the public key, decrypts with the private key and then responds. The private key is never revealed, so if attackers get the public key they can’t do shit with it.
Just be sure that your private key is safe (use a strong master password for your PM vault) and your passkey can’t be stolen by hacking of a website.
I see, that makes sense and should be more secure, in theory. Thanks for the explanation.
The issue I have is, whether I need to trust a third party with my private key, e.g. Google with Android, Microsoft with Windows, etc. (yes on linux it’s different, but that’s not my only OS).
Also if the private key does get compromised (e.g. local malware steals it), hopefully there’s an easy way to revoke it.
Agh, gross.
Proton Pass is open source and the company that runs it recently reincorporated as a Swiss non-profit to ensure their privacy mission can’t be bought out by venture capitalists etc.
Honestly, it’s Bitwarden right now. This move signals their intent to change that, though.
so the “no longer open source” means they’ll be moving to a saas model or something? i’m not super cybersecurity savvy but bitwarden is what i use
It means we have less insight on what they are doing with our passwords.
great…
It doesn’t mean that in this case, except perhaps very indirectly.
No, technically they already are SaaS company. That’s mostly how they make their money.
Also it should be noted “no longer open source” doesn’t mean they’ve done a “our code is now closed and all your passwords are ours” rug pull like some other corporations. This is a technical concern with the license and it no longer meets proper FOSS standards (in other words, it has a restriction on it now that you wouldn’t see in, for example, the GPL).
So by and large the change is very minimal, the code is still available, it’s still the best option. However, this does matter. It may be a sign of the company changing directions. It’s something they should get pushback about.
From the update, it looks like they consider it a bug, which they’re working to resolve. Let’s see how they resolve it before jumping to conclusions.
The SDK was never FOSS, and was never under the GPL. Hence why they can add the text mentioned in the article. You don’t get to change the text of a FOSS license to begin with. It isn’t unheard of for text like this to be part of proprietary software that integrates with and uses FOSS that are under different licenses.
That said, this is concerning, but whether it changes BW’s FOSS state is a matter of legal bickering that has been going on for decades.
You can’t retroactively change FOSS licensing, but oft times you can alter the licensing moving forward. Not always the case, of course. But in no way are all FOSS licenses set in stone.
Sooo, where’s ProtonPass at? They’re open source and non-profit, right?
The server is not open source and I wouldn’t trust a business that is not just working on password managers.
and I wouldn’t trust a business that is not just working on password managers.
Because…? They’re a privacy tool oriented company, no?
Because they aren’t focused on just one single service. Bitwarden is a single business only focusing on their password manager, whereas proton has a suite of tools. Passwords need to be stored absolutely in a robust and safe way. I don’t trust proton with anything at all, and the proton pass is no exception. The client might be open source, but the backend is not. It’s also not as mature as bitwarden.
These are valid points. There are many password managers, most of which it wouldn’t take much to poke holes in, especially if open source is a main criteria.
What are some that you would consider with Bitwarden now being off the table?
Vaultwarden
Its worth noting I don’t think they’re actually a company anymore, I think they’re now a non-profit (I may be mistaken, but that’s my present understanding)
I wonder~ I wonder~ I wonder whyyyy…
I don’t understand.
Are you saying it’s a bait and switch like Google, where they suck people in with a good product then enshittify it once they’re hooked?
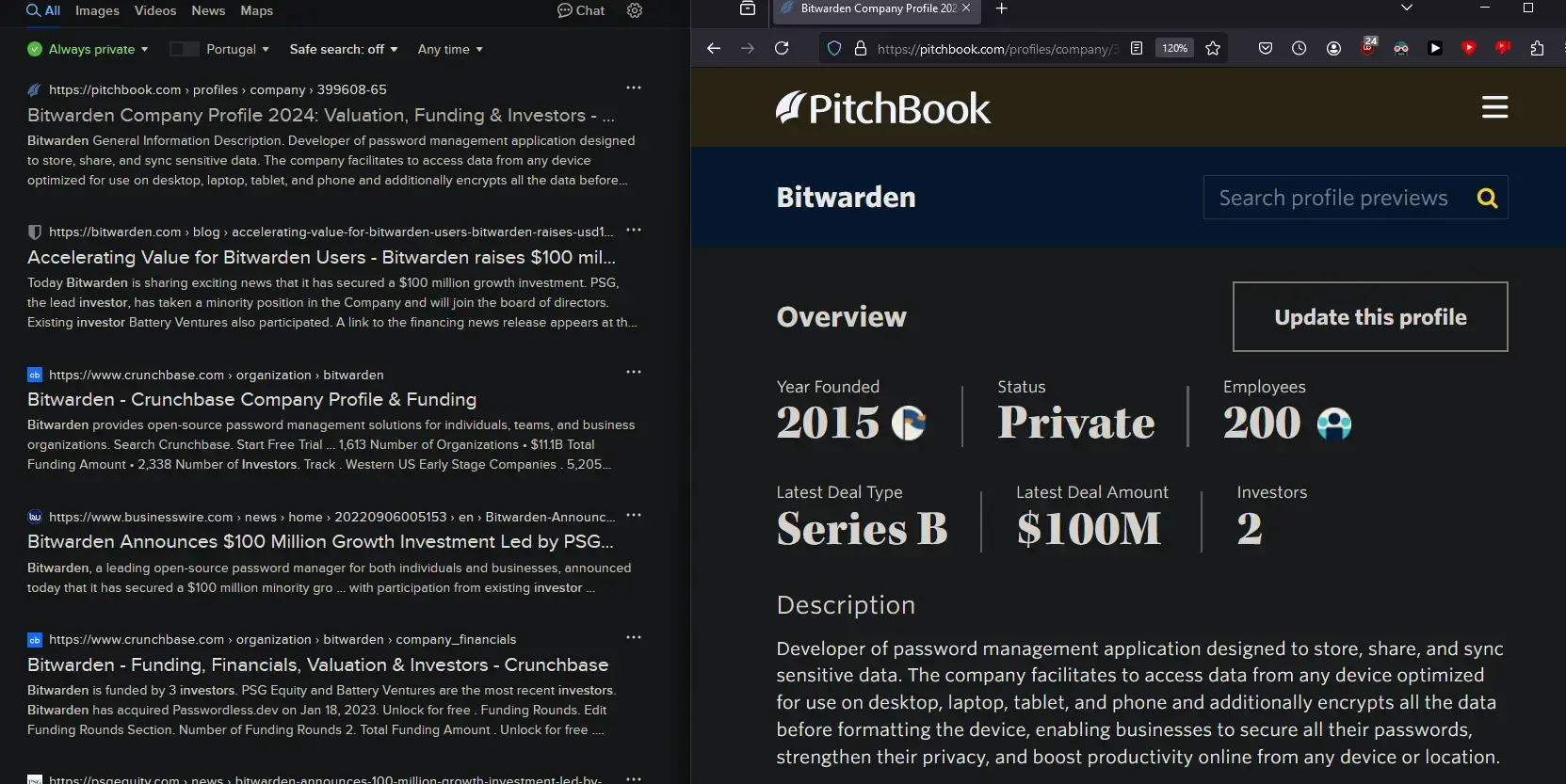
I’m not thoroughly aware of their dealings, but these amounts of private investment aren’t going to pay for themselves. If you raise 100 million, investors typically want a billion back, or more.
From the looks of it, Bitwarden might’ve tried to go with the Open Source model to get free development resources, trust (because it’s an open source PASSWORD manager), and general goodwill. But now that they’ve deemed that got enough of a market share (or investors are starting to breathe down their necks), it’s time to start raising the walled garden.
Even if they claim after the fact that it was a “Bug” that the client couldn’t be built without their proprietary sdk. The very fact one exists is a bad enough sign, specially when its influence is spreading.
VC is a devil’s bargain. Raising VC money is NEVER a good sign.
Yeah well said. Looking forward to the day they try to force an “updated” privacy policy on users, or start charging 69.99/year.
By trying to make things simple, this ends up making it more complicated and convoluted than anything
I like pass and used it for a while, but sharing passwords with it wasn’t nearly as straightforward as it is with bitwarden.
Unix elitist think the average user is willing to just memorize a gazillion different commands. No, nope. Not ever going to use a command line password manager.
Is typing “pass” into a terminal really that much harder than typing <passwordmanager>.com into a browser?
I really don’t know why you think I’m doing that in the first place.
Because unless you paid someone else to set up an account for you, you had to get there somehow. And if you’re using the built in password manager from your browser, none of this article is relevant to you anyway.
have you heard about bookmarks? browser addons? smartphones? URL-checked autofill?
keepass is superior to pass. it even has a CLI.
Yes, that’s why I mentioned account setup. You need to get to the site to bookmark it. And pass has a browser extension too: https://github.com/uri/browserpass
Keepass was where I started before moving to pass and then vaultwarden.
Most people use an extension on web and an app that uses the system autofil functionality on mobile (at least on android, I’ve not used iOS for a long time)
You don’t have to open anything, or type anything other than a password. On mobile you just use your fingerprint, don’t have to type anything at all.
If you’re taking about initial setup that’s also gonna be a lot more complicated for an average user than bitwarden.
A command line tool is not even remotely a comparable user experience. It may work wonderfully for you, and I’m glad it does, but it’s pretty out of touch to suggest that it’d be a good fit for most people
deleted by creator
Vaultwarden updated link
Open source version of bitwarden written in rust.
Where is the foundation to support foss?!?
This is by no means to a slight towards bitwarden. Solid product and community
If they’re moving away from open source/more monetisation then they’re going to do one of two things.
1: Make the client incompatible (e.g you’ll need to get hold of and prevent updating of a current client).
2: DMCA the vaultwarden repoIf they’re going all-in on a cash grab, they’re not going to make it easy for you to get a free version.
Don’t forget option 3: someone writes a vaultwarden client independent of the closed-source crap.
If you can write a server that fully supports the client via the documented API, then you know everything you’d need to do to make a client as well.
That’s not a third option in the same list (things they are going to do), it’s an item in an entirely different list (foss responses to their actions).
You can’t “dmca” the fork that was created while it was still open source. They could only prevent it from getting future updates (directly from them).
DMCA is a tool for suppression of free information. It doesn’t require evidence that you’ve made a good faith effort to consider fair use or other legal complexity as it’s meant to take down the information before that is settled in court, but most commonly used to suppress information from a person or group who can’t afford to fight it in court. Microsoft’s Github has a history of delete first without risking their own necks to stand up for obviously fraudulent takedowns much less ones with unsettled law like APIs/SDKs.
If you mean they shouldn’t. I’d agree. But, as has been seen a lot on youtube. “They” can DMCA anything they want, and the only route out is usually to take them to court.
I mean I’d hope if they’re going in this direction they will be decent about it. But, it’s not the way things seem to be lately.
You have your link formatted backwards. It should be Vaultwarden, with the link in the parentheses.
Well, I guess not having password manager yet did had some benefit because now I know not to use bitwarden
Keepass. Keep it simple.
3rd party sync of the database can have a lot of problems
If you want to roll your own with keepass that’s fine, but most people will want a more comprehensive solution.
I switched from keepass to Bitwarden because individual entries started randomly disappearing. I’m still discovering missing accounts after switching a couple of weeks ago. Sometime to do with how keepass was opening the files, because when an entry went missing it was gone even from backup files I hadn’t touched since before the entry disappeared.
Sound like something you did with replacing files. KeePass is dead simple, and that’s why it’s great.
Nah, the timeline looks like this:
- use account on main
- create backup
- use account on main
- account goes missing from main.
- check backup, account also missing from backup.
Like, it should be in the backup, I proved it was in the original before and after creating the backup. Heck if I know why they went missing.
Update: Bitwarden posted to X this evening to reaffirm that it’s a “packaging bug” and that “Bitwarden remains committed to the open source licensing model.”
According to Bitwardens post here, this is a “packaging bug” and will be resolved.
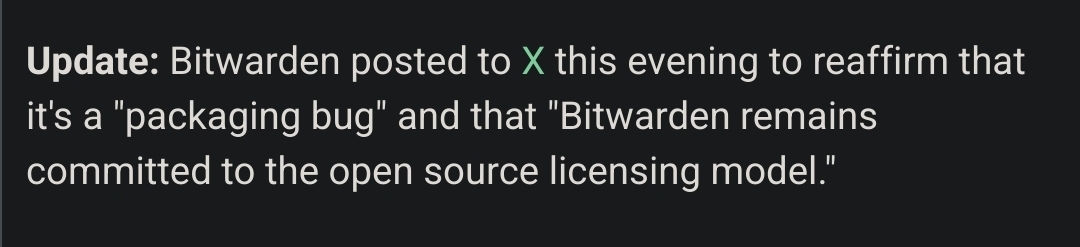
oh thank god
The community’s reaction is a but funny if this was a honest mistake
Goddammit. It’s getting to the point I’m going to have to figure out how to write my own app for this.
Thank you for the update! I would like to keep using it. I’ve been very happy with Bitwarden both as a password manager and a TOTP authenticator. I have even recommended it to my boss as an enterprise solution for us to use at work, and so far we are planning on replacing our current password database solution with Bitwarden.
Unfortunately, with “enshittification” being so common these days, it was very easy to believe they were also going to the dark side. I will remain cautiously optimistic after learning it was a packaging bug.
Here’s a link to the post on X (yes, I hate X, too) in case anyone else is doubtful:
Yeah, I was worried about it too. I’ve become pretty cynical when it comes to everything becoming enshittified, but I’m hoping they stick to their word.
It shouldn’t even be that complex…
I might be mistaken, but ultimately a password manager is basically nothing more than a database of passwords in an encrypted zip file, right? That could entirely be self-hosted with off the shelf open source applications stringed together.
All you’d need is a nice UI stringing it all together.Edit: I’m not sure why people are downvoting me. Is that not what a password manager essentially is?
I’ve done basically this in the past by encrypting a text file with GPG. But a real password manager will integrate with your browser and helps prevent getting phished by verifying the domain before entering a password. It also syncs across all my devices, which my GPG file only worked well on my desktop.
Keepass is exactly that. Basically all the client side parts, and the database is a single encrypted file that you can sync however you want.
It’s the “stringing it all together” that could be problematic.
If you have multiple clients (desktop/cellphone) modifying the same entry (or even different entries in the same “database” ). You need something smart enough to gracefully handle this or atleast tell you about it.
I did the whole “syncing” KeePass and it was functional, but it also meant I needed to handle conflicts - which was annoying. I switched and really appreciate the whole “it just works” with self-hosted bitwarden.
I see it as it’s easy to self host. But I’m not skilled nor rich enough to guarantee the availability of it. I don’t want to be stuck on a holiday without my passwords because my server back home died from black out or what have you.
I pay for bitwarden and the proton mail package to keep the password management market a bit more competitive and it actually works out cheaper. It would be nice to have protons anonymous emails built in, but I can live with it.
But I might have to reconsider if Bitwarden is going a different direction that what I’m paying for.
That is the bare minimum of a password manager like Bitwarden.
Yup, thanks. Was thinking along these same lines.
600 upvotes and only 10 downvotes on literal fake news. I wish readers were less lazy, it’s very frustrating.
Edit: made my statement a bit less toxic. I was mad.
How is it fake news? They are moving functionality into a proprietary SDK and have a whole framework ready to get around the GPL.
deleted by creator
Yes.
To me that just like an excuse for the current mess. Did you read the original GitHub issue? Their CTO also seems to have questionable ideas about the GPLv3.
Community is fine, your comment is at the top, along with others pointing this out.
It’s the “non-community” if you will boosting this. The passerby’s not reading comments.
No one is listening I’m sorry to say. I corrected a couple people but then realized it was pointless. The discussions in the crossposted communities (which - holy shit I don’t think I’ve seen something so thoroughly spammed across multiple tech communities before) are just as bad or worse.
can we start reading the articles and not just the headlines??? it literally says it’s a packaging bug
In general, if it’s Phoronix, I assume the headline is a bit more exaggerated. They put out pretty good content, but they also put out a lot of content, so the editing can be a little lacking IMO.
It is really not just a packaging bug. If you read that comment of the Bitwarden person a little further, you’ll notice that he’s talking about that proprietary “SDK” library that they are integrating with their clients. Even if they manage to not actually link it directly with the client, but rather let the client talk to that library via some protocol - it doesn’t make the situation any better. The client won’t work without their proprietary “SDK”, no matter if they remove the build-time dependency or not.
oh shit i didnt know that, mb man
When I read this this morning, I had concerns, but then I did some research. The SDKs source is fully available for all to look at and compile. The main issue that people bring up is the license that states:
3.3 You may not use this SDK to develop applications for use with software other than Bitwarden (including non-compatible implementations of Bitwarden) or to develop another SDK.This part seems to be what most people take issue with, as it makes the sdk no longer modifiable, yet a requirement of the core source itself. The head of BitWarden has come out and stated the SDK being required to compile BitWarden was a mistake, however, and if this proves to be true (which I have no reason to doubt) then I see no reason why any of this is an issue.
From a security standpoint, since the SDK is source available, it can be audited by anyone still (and compiled) so personally, I’m fine with this.
The head of BitWarden has come out and stated the SDK being required to compile BitWarden was a mistake, however, and if this proves to be true (which I have no reason to doubt) then I see no reason why any of this is an issue.
I don’t see why this should make any difference at all. Sure, I get why he is are saying they are going to fix it - he thinks that this gets them in compliance with the GPLv3. But from a practical point of view there is no difference at all. The software is useless without that SDK part. Even if it does indeed get them in the clear from a legal point of view (which I am not convinced that it actually does), it is still a crappy situation.
I think, it would look way less shady, if they said they are going fully source-available and not pretend that they are keeping the client open source. I would still dislike that, of course. At least that wouldn’t have eroded the trust in them as much as it did for me.
…in the update that came out after this article was posted and the discussion took place.
mb i didnt see the update part
Some guy at bitwarden clicks a button wrong on a license drop-down option and all these people crawl out of the woodwork to declare the end of bitwarden being trustworthy. Nothing in the article or the company’s statements indicates an actual move away from open source. Big nothingburger
Maybe you want to read the comment by kspearrin in that Github issue again. They are clearly moving away from open source. He explicitly states that they are in the process of moving more code to their proprietary “SDK” library.